HID stories - Page 35
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

Most organisations exhibiting malicious RDP behaviour - report

Malware hiding on popular content delivery networks - WatchGuard

HID Global acquires PKI-as-a-service solutions provider HydrantID

Popular enterprise printers riddled with security risks

Banking malware grows 50% while cryptominers decline – Check Point

CrowdStrike report lists cybersecurity adversary rankings

HID Global: Key considerations for secure card issuance

IoT home connectivity on the up, as are cybersecurity threats

10 times malware proved that MacOS isn't bulletproof

Ping's significant expansion of its cloud identity solution
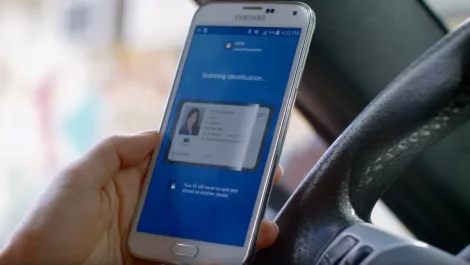
HID Global launches ID verification solution

RapidFire Tools helps MSPs and SMBs navigate cybersecurity liability

Cloud-based ID card issuance will reinvent government processes

Nearly half of all employees are willing to share business secrets

Why one in three CEOs would fire the person responsible for a breach - Nominet

SailPoint launches AI-powered cloud identity platform

How to avoid becoming a cryptojacking victim - Bitglass

Exclusive: Okta CSO on scaling security alongside business growth

Unisys integrates security into Dell EMC Cyber Recovery
